Over the past several years I have communicated with many clients concerning the use of personal technology in their businesses. Employees frequently access company resources using a plethora of devices; cell phones, personal laptops, tablets, etc. In today’s Mobile World, where everyone is being forced to work from home, we’re finding more of these types of devices being integrated into the daily routine of our staff members. The challenges that this presents to the IT department is exhausting.
IT security engineers and support professionals find themselves frequently chasing their tails when it comes to controlling the proprietary information within our businesses. Users must take on a new form of responsibility in regard to their personal protection of company resources. With so many of us working remotely these days, technology security is more critical than ever. We not only need to protect the intellectual property of our employers; we need to protect our own personal devices and information as well.
In a future blog post I will cover the importance of protecting yourself from things you can’t see. That post will describe a hacker’s tool called a Pineapple that can truly ruin your day. However, for now here are some key points for you to keep handy and to pass around to your colleagues and friends. They will help you stay secure and keep the bad guys out of your business.
Personal Security
- Turn off your Wi-Fi before you leave the house or your office.
This is part of the discussion that I will cover later related to the Pineapple. However, this is so that you do not connect to a fake Wi-Fi network inadvertently. In most of these cases you would be connecting to a hacker’s network where they are spoofing commonly accessed Wi-Fi SSID’s. In this scenario they can perform a ‘man-in-the-middle’ attack and capture your login information to any site or application you access. Just turn it off when it’s not needed and turn it on when you know the network you are connecting to is protected. - Do not automatically connect your Wi-Fi to free, unprotected networks.
A very common approach to gain access to someone’s computer is to broadcast common wireless network names and make them available to connect. Your device doesn’t know the difference between a real coffee shop wireless and a fake one. If the name is the same as a previous SSID that your device is connected to, it will latch on and take hold. That’s when the danger begins. If you connect to a free public Wi-Fi service, make sure that you tell your device not to reconnect automatically in the future. The best practice is to immediately tell your device to forget that wireless SSID when you are finished with the network. - Turn off your microphone and camera
The camera and microphone on your desktop computer, laptop, cell phone, or tablet are an easy target for hackers to gain access to your personal information; gaining access to information that they can visually see or hear as you speak.
In most applications on your portable devices, the settings that control your camera and microphone provide the ability to disable or enable access independently unless an application specifically needs that access. Today you can even select options to only allow access when that application is active on the screen.
On your desktop computer however, it may not be that easy. It’s important that these devices are covered or disabled when they are not in use. Most good computer cameras enable a light to indicate when the camera is in use. However, there is a possibility that a hacker could circumvent this as well.
To control access to my camera, I keep a USB hub on my desk where I plug in or unplug the camera on an as needed basis. This would be the most effective way to control this scenario with a desktop computer. With the laptop there are a few more steps required, however, you should identify on your device how to disable them when they are not in use. - Always keep your devices up to date with security patches and system updates.
Unpatched computer systems and electronic devices are the fastest way to allow hackers access to vulnerabilities within your device. When security holes are identified in a device, and patches or updates are made available, it’s critical that these updates are applied to your device to keep them protected. The moment a new vulnerability is identified, hackers begin their mission of exploiting that vulnerability to gain access to your device. Keep your devices up-to-date and patched as soon as the updates are available. Never turn off automatic updates for security patches on your devices. Unpatched systems are the most common reason found when security events have compromised a device. - Password protect your phone – Biometrics if available
Always password protect every device you access. If biometric controls are available on your device, enable them to help ensure that you are the only one who gains access to your device. If you are working with a sensitive computer where the data that you access is extremely sensitive, two-factor authentication is recommended. This would be most easily added to a laptop or a desktop through the use of a software package that prompts for a second form of authentication, such as a text-message-token or biometrics after a password is entered. - Know what’s encrypted and what is not.
Remember that most personal programs such as email connections to your phone are not encrypted. Check with your email and application provider to see if their program creates an encrypted connect when sending and receiving traffic. Then check your email settings to see if your server will allow a HTTPs, Secure SMTP, or a secure POP connection to the server. If your mail settings on your phone show port 80, 25, or 110 you are not encrypted. - Anti-Virus/Anti-Malware/Anti-Ransomware on all devices
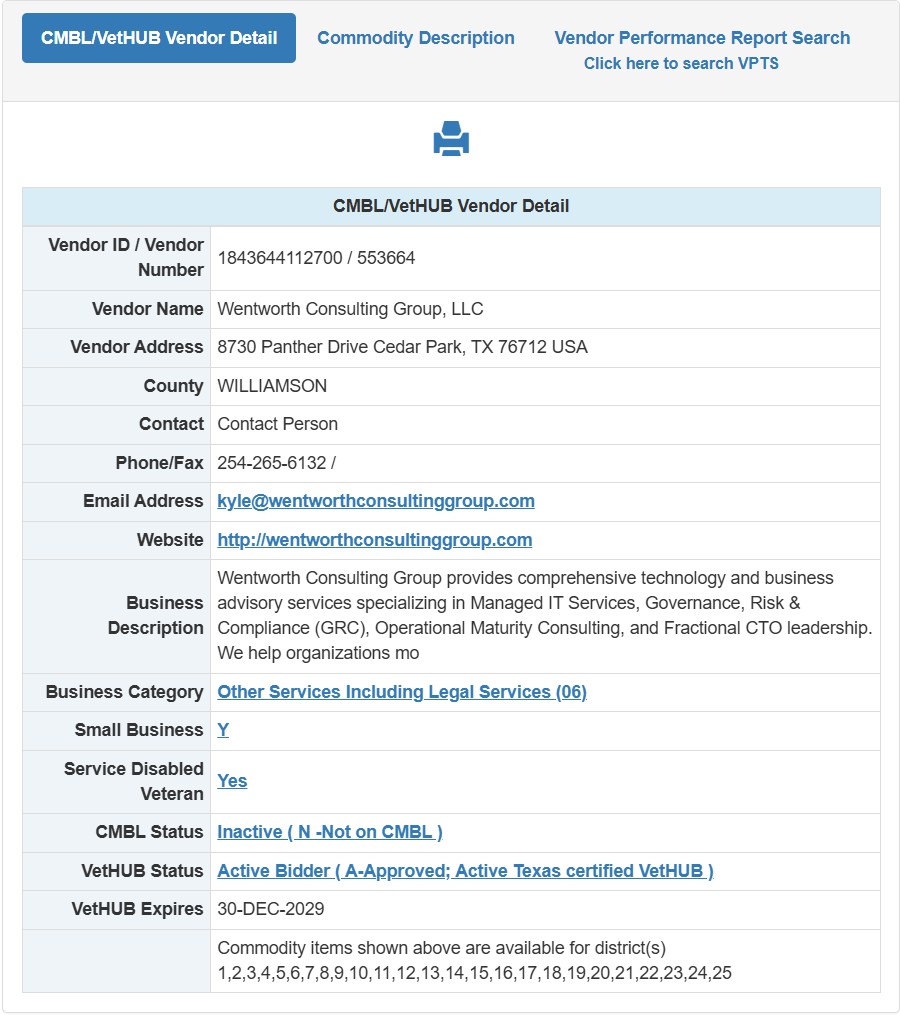
Download, install, and keep up to date an anti-virus/anti-malware program for all of the devices you own. Wentworth Consulting Group currently recommends either BitDefender or Sophos protection solutions for all of your computing devices. One account allows you to protect several devices at the same time through the same management portal.
Let’s stay protected out there and keep the hackers unemployed.